
Automattic is a WordPress giant.
They bring us WordPress.com, PollDaddy, VaultPress, Akisment, Gravatar and a whole lot more! All the while, they contribute to WordPress.org, BuddyPress, WordPress for iOS, Android, Blackberry, WP7 and Nokia!
Busy, aren’t they?
This past week, they had a security breach. In some ways it makes sense. Large organizations tend to be targeted. At the same time, because Automattic knows they are more apt to be hacked, they take amazing precautions to protect themselves.
This past week on the WordPress.com blog, this “security incident” was announced:
Tough note to communicate today: Automattic had a low-level (root) break-in to several of our servers, and potentially anything on those servers could have been revealed.
We have been diligently reviewing logs and records about the break-in to determine the extent of the information exposed, and re-securing avenues used to gain access. We presume our source code was exposed and copied. While much of our code is Open Source, there are sensitive bits of our and our partners’ code. Beyond that, however, it appears information disclosed was limited.
The “investigation” is sill an ongoing matter and is said to take a while to complete. In the meantime, the only recommendation they are giving their users, is a friendly reminder to follow basic security fundamentals:
- Use a strong password, meaning something random with numbers and punctuation.
- Use different passwords for different sites.
- If you have used the same password on different sites, switch it to something more secure.
Automattic’s attack should remind us that anyone is susceptible to identity theft, server attacks, or having your Facebook hijacked by spam messages!
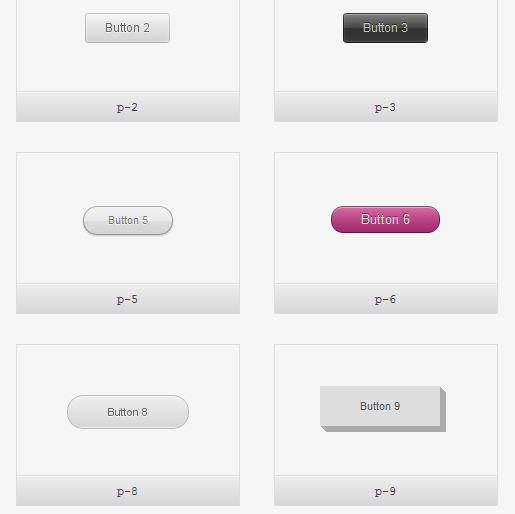
Here are a few links recommended by WordPress.com, to make it easier to keep track of multiple logins:
The cost of being hacked is high, but the embarrassment can sometimes be greater.







Speak your mind...