For many this might be just a bit too much information, but I know there are a few of our readers out there who really appreciate the in-depth looks at hardware and software.
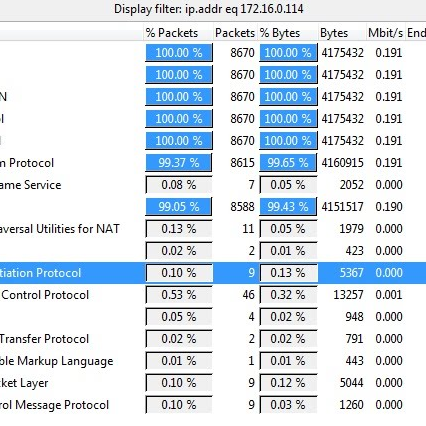
I found a great article on the new iPhone4 FaceTime protocol that was extremely interesting and brought up some intriguing questions on exactly how this is accomplished, some of which I had not thought of previously. For example:
- How is the management and streaming traffic protected?
- How is the call authorized by the end-user?
- What can we deduce by sniffing the WiFi-side of a Facetime transaction?
Good questions.