We’ve discussed before about making sure that you utilize https when surfing the intertubes from open wifi networks. Mainly like the ones found at local coffee shops.
But what happens when you are just not able to? When the server you are contacting doesn’t utilize any form of encryption?
Read on for a technique I use when I need an extra layer of security.
The Problem
Just to reiterate, the problem with surfing the internet on an open wifi network is that it is very insecure. Anyone can be on that very same network sniffing your traffic. Most importantly for bloggers, their username and password that they use could easily be stolen putting their blog’s security in jeopardy.
The Solution
One solution that I utilize is to create a ssh tunnel to encrypt my traffic. Now I can do this from the command line in OSX, but a handy tool I’ve stumbled across for this setup is SSHTunnel.
The Setup
You will need access to a ssh server. Contact your web/tech person to see if maybe the server where your blog is hosted has a ssh service available.
1. Download and install SSHTunnel
Open the application
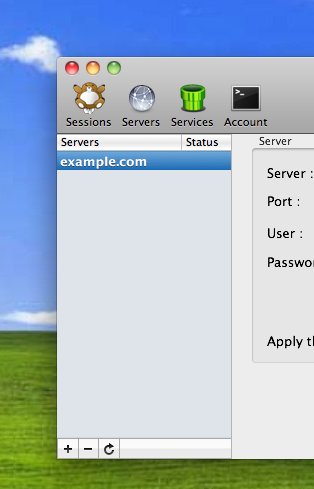
Click the “Servers” icon
Click the “+” plus button and type in a name for your server
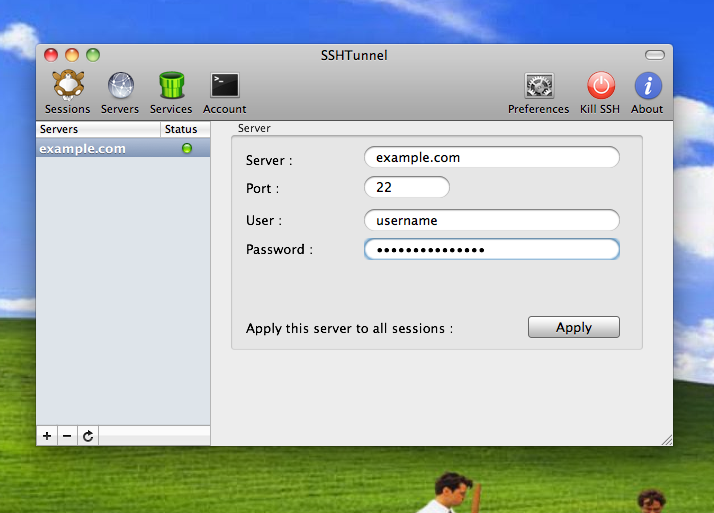
Then add the setup information for your ssh server
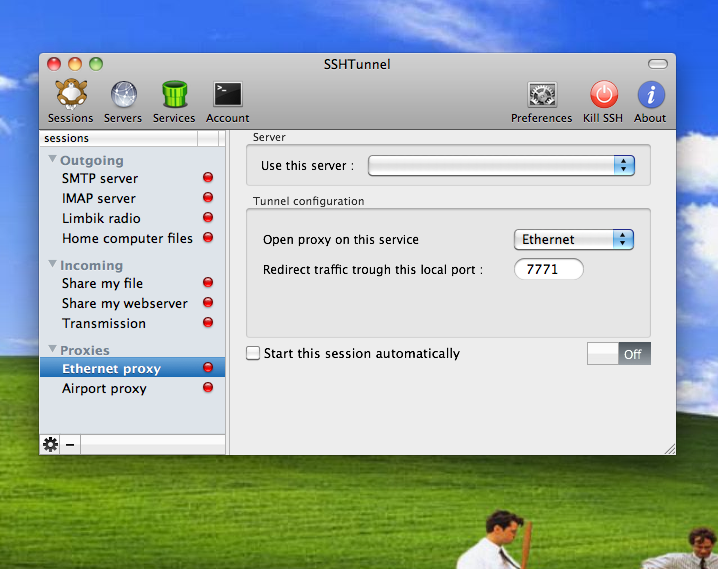
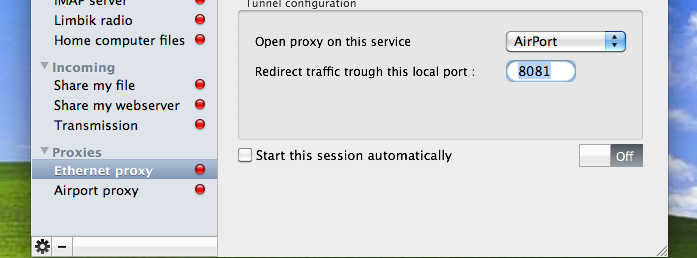
Click by on the “Session” icon and select “Ethernet Proxy” and make sure your server is selected from the drop down.
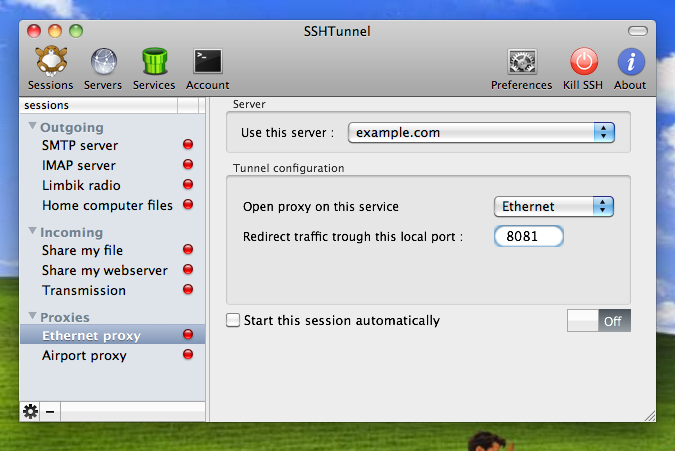
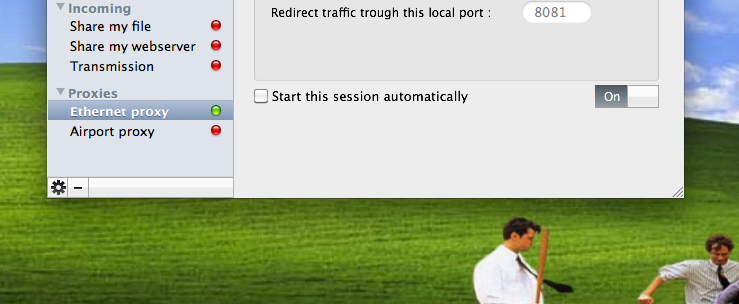
If you are using a wifi network, make sure that you setup the proxy for airport and then also change the redirect traffic port to 8081
Finally, click on the ON/OFF slider button to turn the ssh proxy on
And thats it, your ssh tunnel should be all setup and your traffic is now being encrypted.







Speak your mind...